Cerberus Server Monitor
The cerberus server monitor watches a Nexus server for evidense of tamperring or of things gone quite wrong. Download the service and the configurator place in C:\nexus.
To configure, run cerbconf.exe. Note, its settings are not saved until you click save. Also, you can cut&paste from most text areas by right clicking the mouse.
A
word of wisdom: don’t enable all sorts of warnings or you will start
ignoring the messages. Just check
ones which really frighten you, like disk space, Authenticode, etc. If you start receiving unwanted
messages, uncheck the category creating the noise.
The first section is general.
You can specify the frequency of system checks in minutes. Specifying 0 will cause cerberus to execute every 5 seconds, this is useful for testing.
Beep when run causes cerberus to beep after every run.
Notify
The notify section allows one to set the Email or Syslog addresses. If you enable syslog, remember to set the correct facility for your server. It tries to send the Email through engmail.uwaterloo.ca. That will not work outside of uwaterloo.ca, the current fix is to add a registry setting. Here's the regedit file to change it:
---
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SOFTWARE\Policies\UWaterloo\Nexus\cerberus\general]
"EmailSMTPServer"="gmail.com"
---
Local Groups
This allows one to monitor who is a member of various local groups. Administrators and power users are often worth watching.
AD Groups
AD Groups refer to active directory groups. It is useful to watch Administrators for new members. Note, you have to enter a binding userid and password, which should be for a non-privileged account. Warning, the AD password is stored in the registry, so used unprivileged account names, and enabling this feature adds 3 MB to the cerberus memory footprint.
Files
This is used to watch
subdirectories for changes. Exclude subdirectories or files which you
expect to change.
The files section is still under construction.
Services
The checkbox configures whether services are watched. Ignore is used for services such as the Windows installer - unless you are worried about software being installed.
Log
The log section shows the results from only the most recent run of cerberus. It gets cleared at the next runthrough. This is useful for debugging.
Scripts
The script section allows one to schedule a script, but without having to use the klunky scheduled tasks - allowing one to program it entirely with registry edits. The TEST button tells cerberus to run the script at the next passthrough.
Memory
The memory section allows one to watch a machine for available global memory - such as when a server starts running out of resources. Also, the cerberus memory checker lets you keep an eye on the cerberus memory heap, to see it doesn't start taking up too much ram.
Sockets
The sockets section keeps track of listenning TCP sockets. It can be useful for detecting hacked systems. It keeps track of the application connected to the socket too.
Disk
The disk section keeps track of used space on hard drives. For servers, it is a good way to look for databases growing too big, or hacked systems with large file repositories.
Shares
Monitor shares for unexpectedly connected users.
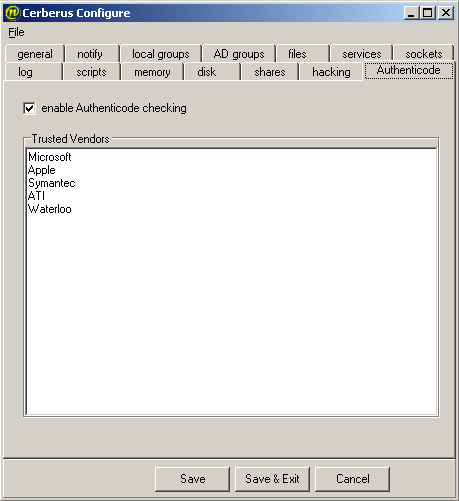 Authenticode
Authenticode
If you check the AUthenticode checkbox, cerberus will note system services
by any company other than the ones you enter.
On my workstation, the only vendors I had to enter were
- Microsoft
- Apple
- Symantec
- ATI
-
You can determine your required list by checking the Email Cerberus sends when it first runs.
Driver Installation
Next it is time to install the cerberus service. Copy cerberus.exe to c:\nexus, run cerberus /install, then using the Windows service manager, start the service after selecting automatic, or just run net start cerberus.
Everytime the cerberus service starts or detects a change, it will email to the address specified in the general section.